Discover
Go beyond traditional SCA capabilities to continuously track all your open-source components and their associated risk, across the SDLC.
See it all clearly, act faster
Go beyond traditional SCA with Rezilion’s Dynamic SBOM: More visibility, less noise; more security at less cost. No agents required.
Know your components
Deploy agentlessly and quickly identify specific OSS components (such as Log4j) within your environment to manage supply chain risk at any stage in the SDLC.
Understand impact
Enhance scan results with intelligence feeds and dynamic runtime analysis data to keep track of your software attack surface as it changes over time.
Achieve compliance
Instantly create and share SBOM and VEX inventory documentation necessary to comply with government software supply chain regulations.

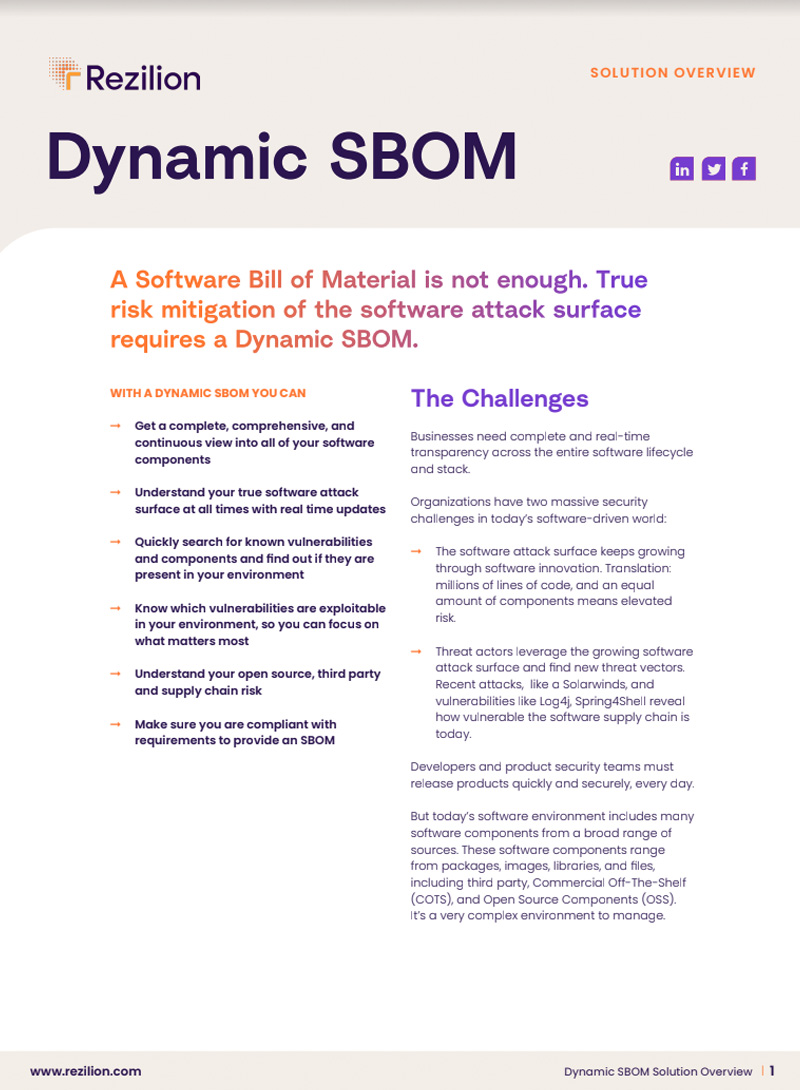
SCA and Dynamic SBOM Features
Full visibility,
full cycle, no agent necessary
Create a live inventory of all third-party software components in your CI/CD, staging and production environments.
- Deploy agentlessly in minutes; simply connect in a cloud provider account and run
- Create a comprehensive inventory of all your software components
- Continuously update your SBOM throughout the SDLC
- Eliminate any coverage gaps
Know your real
attack surface
Understand your changing software universe through real time updates to the SBOM.
- View components with granular precision, down to the function level
- Understand exploitability with runtime analysis
- Know your true attack surface
Search for vulnerable components
Instantly look up any component in your software and know risk associated with them.
- Search for known vulnerabilities such as Log4j
- Instantly analyze if any of the discovered vulnerabilities are exploitable
- Quickly address any risk posed by these vulnerable components
Share your SBOM
Proactively assure customers and communicate true risk in their environment.
- Share a VEX (vulnerability exchange) document to outline impact of vulnerabilities
- Export as a CycloneDX, SPDX or Excel document
- Confidently share your dynamic SBOM with customers for transparency and compliance
Control your software supply chain
Know where every component came from and understand their impact to manage supply chain security.
- Know your open source components and their dependencies
- Find out where each component came from
- Manage license risk associated with each component
Proactively assure your customers
Communicate important vulnerability information with your customers using a formal VEX (vulnerability exchange) document to outline the actual impact of vulnerabilities they may detect in your product.