Analysis: Microsoft Patch Tuesday Update for March, 2023

Microsoft March “Patch Tuesday” Addresses 86 Security Vulnerabilities Including 2 Known Exploited Vulnerabilities.
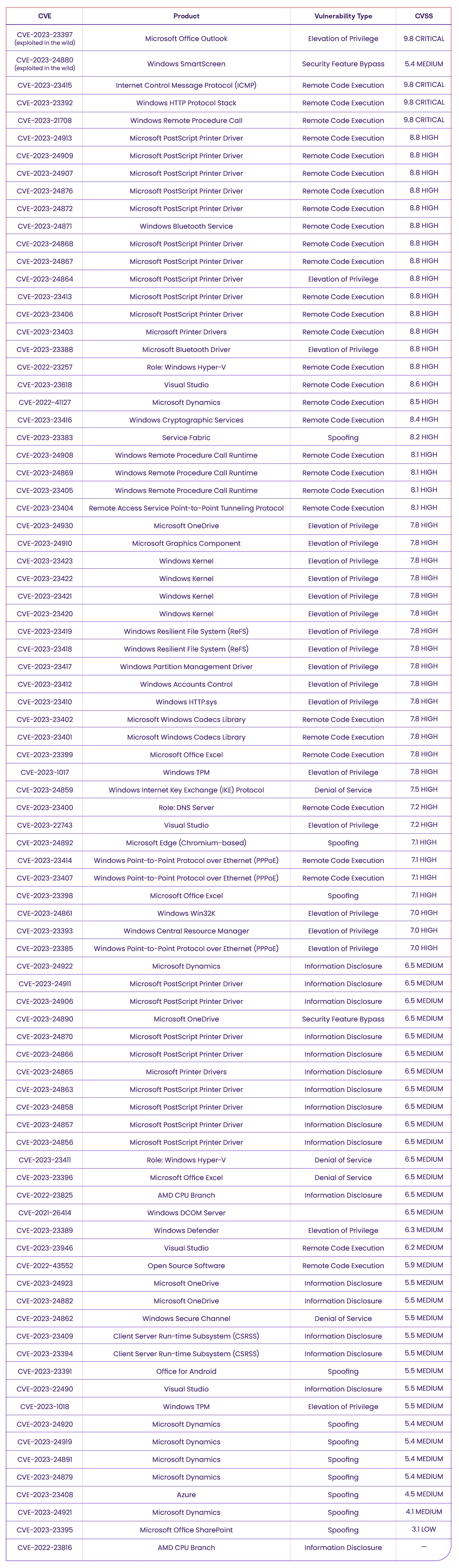
On March 14th, 2023, Microsoft released their March Patch Tuesday security update, and revealed 80 vulnerability fixes, including six updates to old CVEs and two Known Exploited Vulnerabilities (KVEs).
The vulnerabilities affect popular platforms such as Azure, ICMP, Microsoft Excel, Microsoft Outlook, Microsoft SharePoint, and more. According to the National Vulnerability Database (NVD), four of the vulnerabilities are CRITICAL severity vulnerabilities, 47 are HIGH severity vulnerabilities, 33 have a MEDIUM severity CVSS score and one is ranked as LOW severity, and one still did not get a CVSS score.
In this post, we will share details on the vulnerabilities included in the update, and provide recommendations for how to address these risks.
CVE Details
The following table shows information about the vulnerabilities found:
Affected Software Details
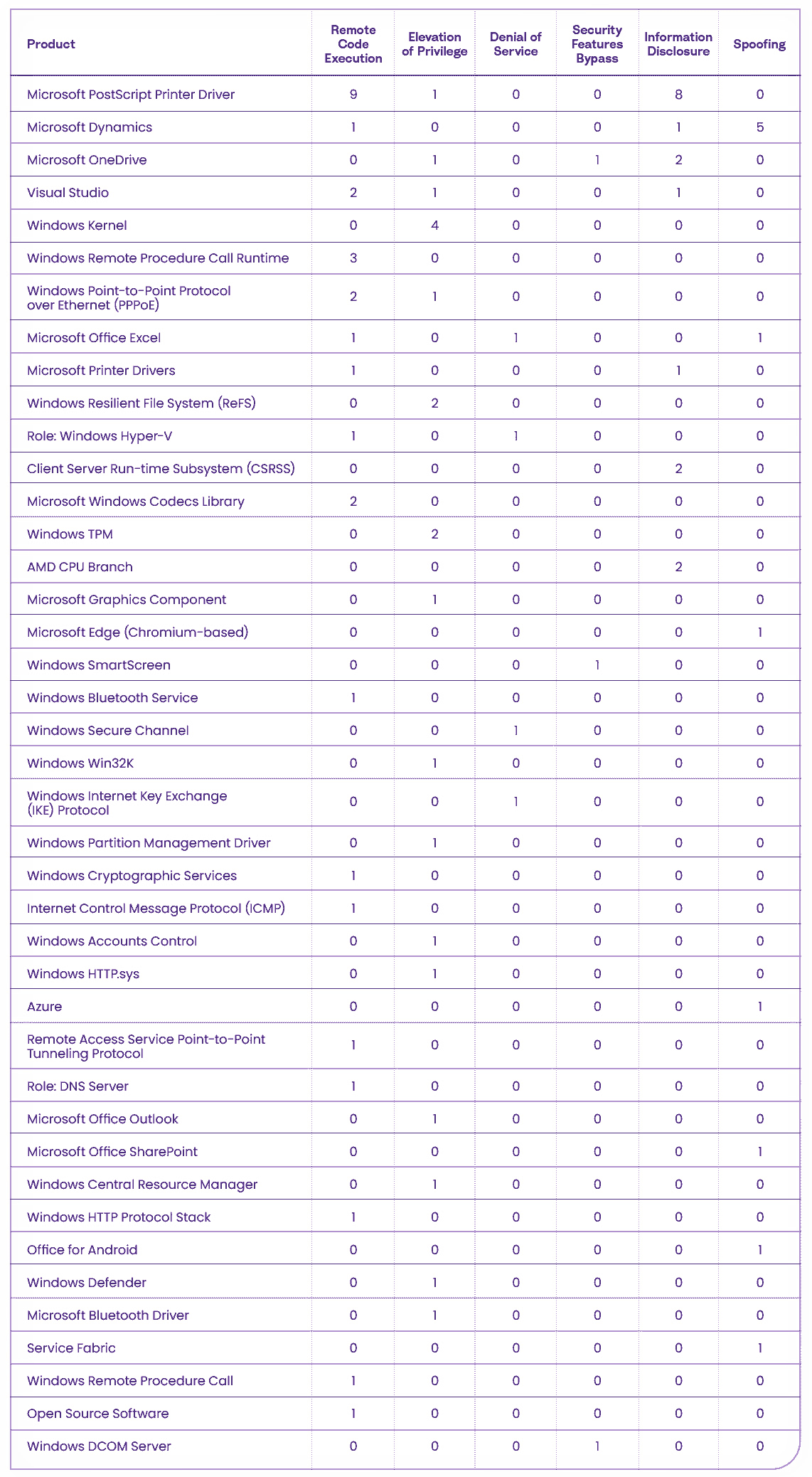
The following table shows a breakdown of the affected software components according to the type of vulnerability patched:
As you can see, the following products have the highest number of vulnerabilities:
- Microsoft PostScript Printer Driver (18) – a Microsoft standard printer driver for PostScript printers.
- Microsoft Dynamics (7) – intelligent business applications that deliver alerts and notifications via Microsoft Teams or Outlook
- Microsoft OneDrive (4) – a file hosting service operated by Microsoft
- Visual Studio (4) – an Integrated Development (IDE) for Microsoft.
- Windows Kernel (4) – the computer program at the core of a computer’s operating system
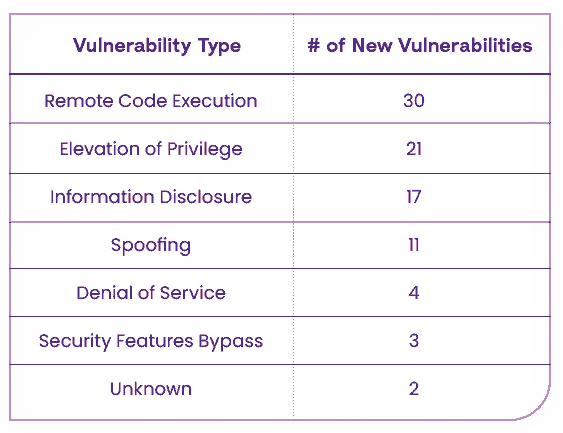
Vulnerability Types
Total number of vulnerabilities by type:
Known Exploited Vulnerabilities (KEVs)
The following vulnerabilities are known to be exploited in the wild and require extra attention:
CVE-2023-23397 – LPE in Microsoft Office Outlook
A 9.8 Critical vulnerability in the Microsoft Office Outlook PidLidReminderFileParameter property, which accepts file names.
Attackers can exploit the vulnerability by creating a malicious calendar appointment in Outlook that includes specific properties, such as PidLidReminderOverride and PidLidReminderFileParameter, which can be modified to include a UNC path instead of a file name which will trigger a NTLM authentication. When a victim opens the email containing the malicious calendar appointment, Outlook immediately triggers an NTLM authentication request to the specified IP address. The attacker will gain the user’s privileges and will be able to access sensitive information and perform malicious actions.
CVE-2023-24880 – Security Feature Bypass in Microsoft Windows SmartScreen
A 5.4 Medium vulnerability in the Microsoft Windows SmartScreen Mark of the Web (MOTW) defenses.
The vulnerability allows attackers to create files that bypass MOTW defenses, which are used by protective measures such as SmartScreen and Protected View in Microsoft Office to prevent the spread of malware. This vulnerability makes it easier for attackers to spread malware through crafted documents and other infected files that would typically be stopped by SmartScreen. The vulnerability is a new variant of the CVE-2022-44698 and results in a limited loss of integrity and availability of security features that rely on MOTW tagging.
Recommendations
If you have any of the affected products listed above in your environment, make sure to patch your system immediately. Additionally, teams should prioritize patching the two Known Exploited Vulnerabilities, which now pose the highest risk of all the vulnerabilities included in this week’s “March Patch Tuesday” update.