CVE-2023-34362 – MOVEit Transfer Zero-Day SQL Injection Vulnerability Actively Exploited in the Wild

Progress Software has recently (May 31st, 2023) released a security advisory regarding a critical zero-day vulnerability affecting ALL VERSIONS of the company’s MOVEit product which is being actively exploited in the wild in order to exfiltrate data from targeted environments.
The vulnerability has been already added to the CISA KEV (known exploited vulnerabilities) catalog.
Note: Updating to a patched version (see remediation section below) will help protect against future exploitation, yet patching alone will not address cases in which threat actors have already exploited the vulnerability to gain access to the target environment.
Hence, employing incident response procedures and trying to identify indicators of compromise is highly advised.
The vulnerability, which was assigned CVE-2023-34362 on June 2nd, 2023, appears to be an SQL injection vulnerability affecting the MOVEit Transfer web application that could allow an unauthenticated attacker to gain unauthorized access to MOVEit Transfer’s database and consequently, depending on the database engine used, execute SQL statements on the target DB. Evidence suggests that the vulnerability has already been exploited in the wild at least from May 27, 2023, leading to unauthorized access to the environment, privilege escalation as well as deployment of web shells that can be later used as a backdoor to the system.
While the full technical details of the vulnerability are still unfolding, Mandiant has performed a technical analysis of the exploitation webshell payload and detailed potential motives (most likely extortion). Microsoft is attributing the attacks exploiting CVE-2023-34362 to Lace Tempest (AKA FIN11, TA505), known for ransomware operations & running the Clop extortion site.
Attack Surface for the MOVEit Transfer Vulnerability
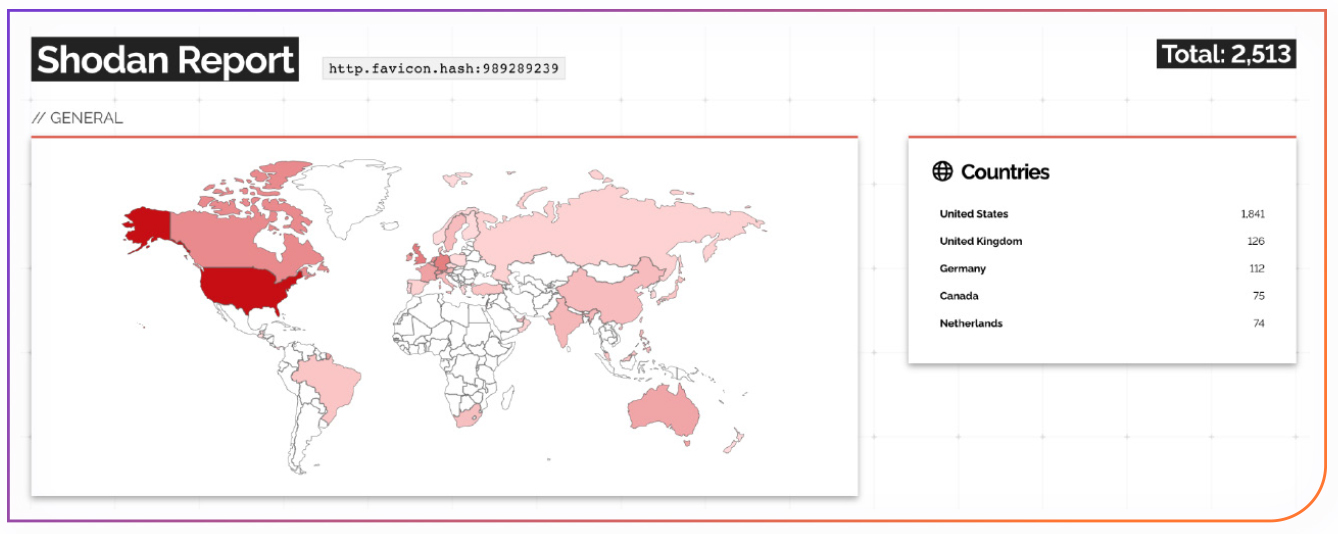
According to the Progress advisory, the vulnerability affects all available versions of MOVEit Transfer including their SAAS offering, which pushed the company to shut down portions of their cloud service as a cautionary means until they developed and deployed a patch.In terms of potential attack surface, a Censys search currently results in 3,559 different IPs running MOVEit Transfer while a Shodan.io search provides over 2,500 unique instances:
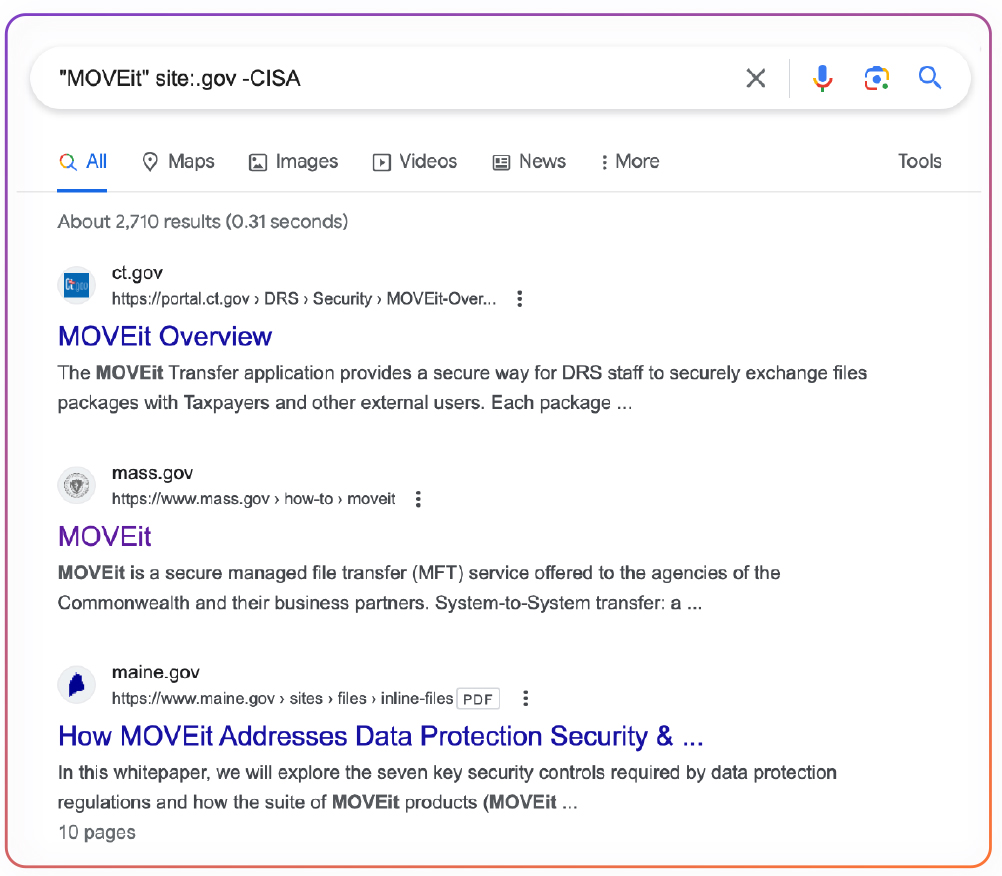
As can be seen in the above image, the majority of the instances are in the US. Since MOVEit is quite expensive it is more likely to exist in large organizations including financial and government institutes. As a reference, by using the following Google dork: site:.gov “MOVEit” we get over 2700 results referencing MOVEit in government sites.
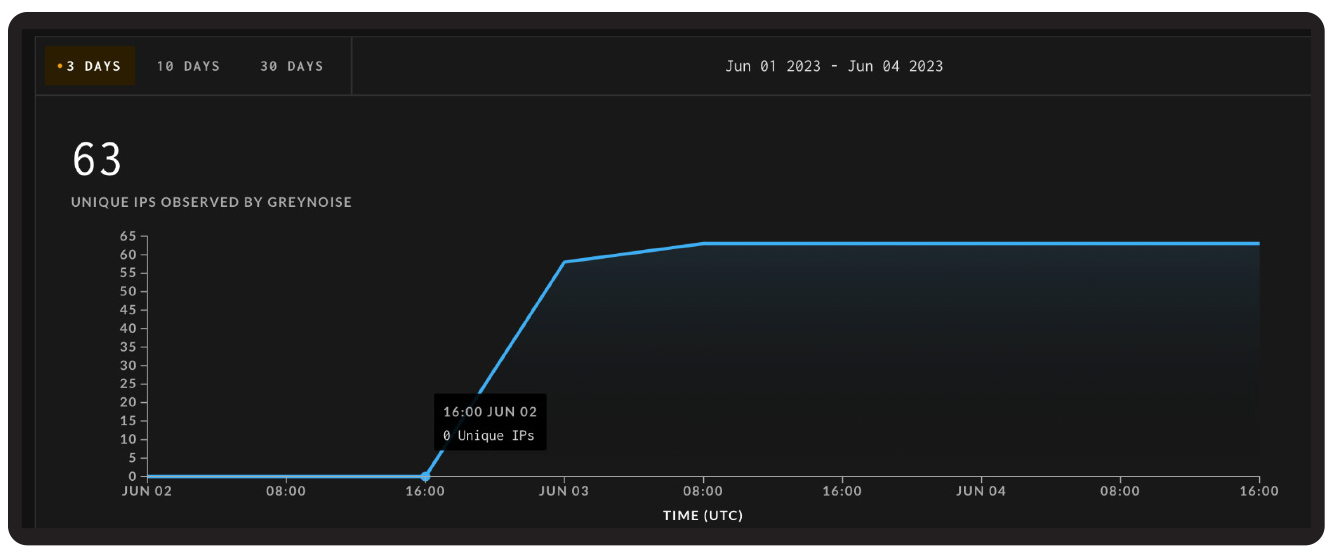
According to GreyNoise, active scanning attempts for the presence of the human2.aspx webshell dropped as part of the post-exploitation activity has been identified as early as March 3rd, 2023. Hence, MOVEit Transfer users are advised to review potentially malicious activity in the last 90 days. It also appears scanning has been renewed starting June 2nd and is still ongoing:
Remediation for MOVEit Transfer Vulnerability
If you are running MOVEit Transfer, apply a patch immediately!
Progress has released patches for all affected versions of their product, including a patch for the retired version 2020.1.x (users running older versions should immediately upgrade to one of the supported patched versions), and are recommending users take the following steps:
- Disable all HTTP and HTTPs traffic to your MOVEit Transfer environment
- Follow Incident Response procedures (see below).
- Apply the patch
- Enable all HTTP and HTTPs traffic to your MOVEit Transfer environment
- Verify no indicators of compromise exist and continue to monitor network, endpoints, and logs for IoCs.
List of available fixed versions:
Note: MOVEit Transfer users who happen to use the Microsoft Azure integration are also advised to rotate their storage keys.
Mitigation
If you are running MOVEit Transfer in your environment yet for any reason you are unable to apply the patch follow the above-mentioned steps and make sure to:
- Update network firewall rules to only allow connections to the MOVEit Transfer infrastructure from known trusted IP addresses or block HTTP traffic on ports 80 and 443 altogether.
- Review and remove any unauthorized user accounts.
- Update remote access policies to only allow inbound connections from known and trusted IP addresses
Incident Response
Since active scanning and exploitation is known to take place, assume compromise, and follow the following guidelines:
- Remove network connectivity / perform network segregation (contain)
- Check for and delete any newly created or altered .asp* files, including any instances of human2.aspx or _human2.aspx and .cmdline script files.
- On the MOVEit Transfer server, look for any new files created in the C:\MOVEitTransfer\wwwroot\ directory.
- On the MOVEit Transfer server, look for new files created in the C:\Windows\TEMP\[random]\ directory with a file extension of [.]cmdline
- Remove any unauthorized user accounts.
- Review logs for unexpected downloads of files from unknown IPs or large numbers of files downloaded.
- Retain a copy of all IIS logs and network data volume logs. Review the IIS logs for any events including GET /human2.aspx. Large numbers of log entries or entries with large data sizes may indicate unexpected file downloads
- If applicable, review Azure logs for unauthorized access to Azure Blob Storage Keys and rotate any potentially affected keys.
- Reset service account credentials for affected systems and MOVEit Service Account.
About the author: Yotam Perkal is the lead vulnerability researcher at Rezilion, specializing in vulnerability validation, mitigation, and remediation research. He brings extensive expertise in vulnerability management, open-source security, supply chain risks, threat intelligence and fraud detection (with 8 patents in those domains). Yotam is an active member of various OpenSSF working groups, focusing on open-source security, as well as several CISA work-streams on SBOM and VEX.